Industrial Network Security
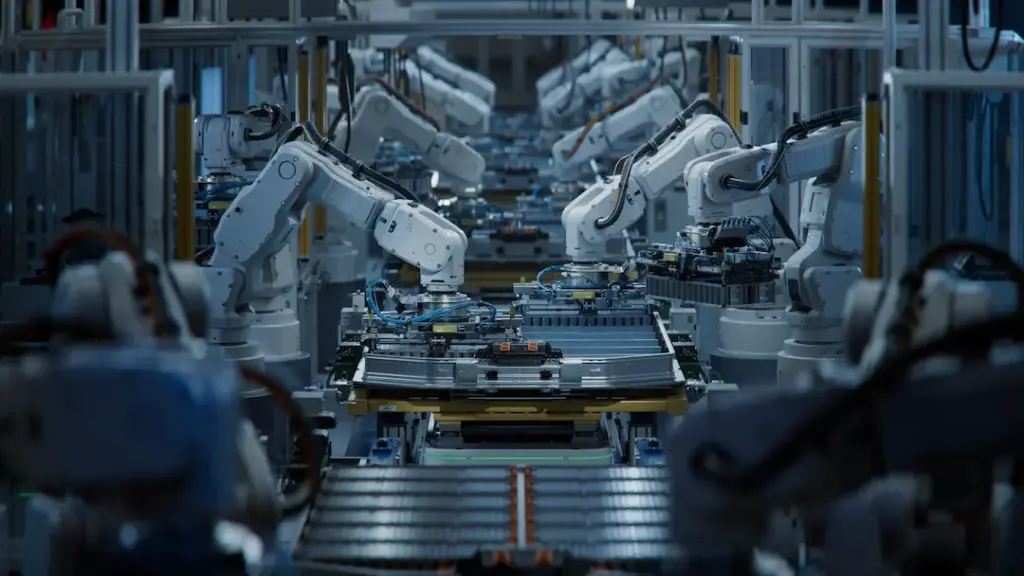
Our Industrial Network Security service protects critical industrial networks and systems (ICS, SCADA, OT) from cyber threats while ensuring compliance with NIS2 directives. Today, a security incident can impact not only data but also halt production, damage equipment, and create risks to employee safety and the environment.
NIS2 requires organizations to implement advanced technical and organizational measures to protect critical infrastructure, detect incidents quickly, and report them promptly. Our service combines continuous monitoring, network segmentation, strict access control, and international industrial security standards to protect ICS/OT networks, ensure operational continuity, reduce risks, and prepare organizations for NIS2 audits and compliance.
What This Service Covers
Industrial network segmentation and isolation
We implement dedicated segments for ICS/SCADA, with strictly controlled policies and industrial firewalls (ICS Firewalls). Segmentation not only limits the spread of incidents between critical zones but also provides clear visibility of traffic and system behavior, facilitating rapid vulnerability identification and meeting NIS2 audit requirements.
Securing OT and ICS equipment
We assess and secure all critical industrial equipment, including PLCs, HMIs, and RTUs. We apply hardening practices, regular patch management, and granular access policies tailored to each industrial operating system. Additionally, equipment is maintained resilient against known exploits and prepared for complex attack scenarios, reducing downtime and operational losses.
Industrial communications security and data protection
We protect data flows between ICS devices, control servers, and SCADA systems through encryption, secure authentication, and packet integrity. This prevents interception, tampering, or corruption of critical data, ensuring that production information, process parameters, and industrial logs remain secure and compliant with international standards.
Backup, redundancy, and operational continuity
We provide encrypted backups for critical configurations, replication, and disaster recovery plans validated periodically. These measures ensure continuous operation of industrial infrastructure, protecting production lines and minimizing the impact of any incident on operations and NIS2 compliance.
Access management and privileged users
We implement strict controls for operators, engineers, and external vendors. Multifactor authentication, role-based access control (RBAC), and continuous auditing of privileged actions significantly reduce the risk of unauthorized access or human error compromising critical systems.
Why It Matters
Industrial networks and ICS/OT systems are the backbone of critical infrastructure in large organizations. Without adequate security measures, these networks are vulnerable to cyberattacks that can lead to production stoppages, equipment damage, significant financial losses, and direct risks to employee safety and the environment.
NIS2 requires essential entities to implement specific technical and organizational measures to protect critical infrastructure and respond fast to incidents. Without solid protection, organizations risk significant penalties for non-compliance, audit challenges, and failure to report incidents promptly.
Our Industrial Network Security service ensures that critical networks are properly segmented, continuously monitored, protected against internal and external attacks, and ready to respond rapidly to any event, providing a balance of safety, operational continuity, and NIS2 compliance.
How Our Service Works
Assessment and
ICS/OT mapping
We evaluate industrial network architectures, identify risks and vulnerabilities, and map NIS2 requirements onto existing infrastructure.
Industrial security design and implementation
We build network segmentation, deploy industrial firewalls, perform equipment hardening for ICS devices, and enforce strict access policies.
Continuous monitoring and
detection
We implement SCADA/ICS monitoring solutions, analyze abnormal behaviors, and alert the security team in real time.
Continuity management and
backup
We provide replication and backup for critical equipment and disaster recovery plans validated periodically.
Audit and continuous
optimization
We conduct internal audits, test controls, and optimize security measures to remain compliant with NIS2 and international industrial best practices.
Key Benefits
Complete protection of industrial networks and ICS/OT systems
Guaranteed NIS2 compliance and audit readiness
Reduced risk of downtime and financial loss
Early threat detection and rapid response
Advanced access control and network segmentation
Periodically validated backups and operational continuity